In a previous post Understanding Conference Security in Lync Server 2010, I detailed the difference between public and private meetings, how assigned conferences work in Lync and the user experience. When you first deploy and configure Lync, users schedule meetings with the same meeting join URL and conference ID every time. However there are some scenarios where this ease of access exposes a vulnerability, especially if there is heavy conference usage. In this post, I’m going expand to on my last post to cover the business reasons why you’d want to configure unique URLs/conference IDs and what the pros and cons are of configuring this. Continue reading
Category Archives: Conferencing
Lync Conference Expiration and Deactivation Explained
I came across this recently when I had to conduct a bit of a deep dive into how Lync conferences behave when they effectively reach “end of life”. In the first instance, I managed to find this about conference expiration in Office 365:
• For a one-time scheduled meeting, the expiry time is the scheduled end time plus 14 days.
• For a recurring scheduled meeting with an end date, the expiry time is the scheduled end time of the last meeting occurrence plus 14 days.
• For an ad hoc IM or A/V conference, the expiry time is 8 hours.
• For a recurring scheduled meeting without a specified end date, the expiry time is 6 months after the last meeting activation.
To clarify, meeting activation is whenever a conference is accessed by a participant.
These settings apply to Lync on-premises also, but I wanted to know if they could be modified. I knew I’d seen something mentioned about modifying when conferences end, and Brian Ricks reminded me of Set-CsUserServicesConfiguration. With this cmdlet, we can set a parameter -DeactivationGracePeriod that allows us to set the maximum amount of time that a meeting can remain active. However, this was only half of the story.
Deactivation and expiration are related, but different.
Deactivation is when the server will forcefully shut down a meeting. It’s like a server-driven version of the exit-and-end-meeting presenter command. However, you can immediately reactivate a deactivated meeting. This is just a brake on runaway meetings, so if someone locks their workstation and goes on vacation while signed into a meeting the meeting will eventually end. It’s meant to be an “infinity” value. You set it just higher than you expect a real meeting to last.
Expiration is when the server deletes the meeting, its contents, and coordinates (i.e. the link won’t work anymore). Expiration can’t happen while a meeting is activated, and there are grace periods based on the meeting type and scheduled end date. The grace periods are to give time to download meeting data (like uploaded handouts or whiteboards) before it’s deleted.
So, conference deactivation is when Lync will end an active meeting so it doesn’t sit there and take up server resources unnecessarily. It’s controlled using the cmdlet I mentioned above (Set-CsUserServicesConfiguration). Conference expiration however is hard-coded behaviour based on the type of conference that’s been initiated and means the absolute end of a meeting. This means the meeting URL and conference ID cease to work and all meeting content is deleted.
Interesting stuff to know. Credit to CJ Vermette from Microsoft for explaining this and clarifying how the two behaviours are different.
Understanding Conference Security in Lync Server 2010
By default, Lync provides a pretty open conferencing experience for users. It allows a fair degree of flexibility in terms of functionality after you’ve first deployed it; and I suppose this is to provide the most complete experience to users when they first try it out. In this post, I’m going to talk about why we would want to modify this default behaviour and how we can make Lync conferences more secure. The two main default behaviours that would make you want to increase conference security are:
- The same meeting URL and conference ID is assigned for the user for every meeting by default.
- PSTN callers will bypass the lobby when they join a meeting and do not need to be admitted to the meeting by a presenter. This contradicts the behaviour of a lot of audio conferencing providers today, where everybody must wait for the leader to arrive until the conference begins.
Together, these behaviours may represent a security risk to some organisations. Let’s go through how we can mitigate them. Continue reading
How do I configure entry and exit announcements for Lync audio conferences?
One of the great new conferencing features introduced in Lync Server 2010 was the ability to play entry and exit announcements in audio conferences. Along with having participants record their name upon joining, this functionality brings Lync even closer to replacing traditional dial-in conferencing bridges.
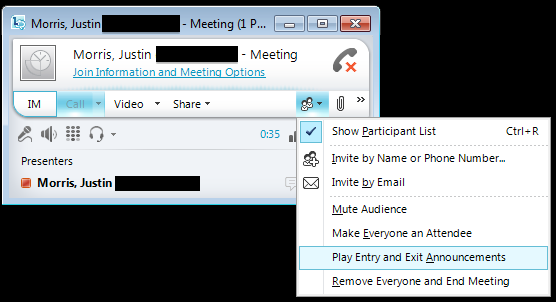
However out of the box, Lync conferences don’t play entry and exit announcements by default. The option is available in the Lync conference but the presenter must turn this on when they begin the meeting as shown below.
This provides a lot of flexibility to the individual conference organiser, but a lot of organisations want this behaviour to be on by default for all conferences. In this post, I’ll cover how to configure this in Lync Server 2010. Continue reading
Support for Large Meetings (up to 1000!) on Microsoft Lync Server 2010
A quick one to let you know that Microsoft have just released a document with advice on how to configure your Lync Server 2010 environment to support large meetings.
Previously the hard limit was always 250 participants per meeting. That was increased not too long ago to 1000, but there was no guidance regarding how you could plan or scale your environment for this, until now.
The catch is, you need a dedicated Front End pool for the meeting, and only one meeting can occur at a time. No users, no other services on it at all. I can see the reasoning behind this to achieve the best user experience but personally, I’d probably be sticking to the Live Meeting service if I needed to host meetings of this size.
When it comes to what can be presented in the meeting, we’re talking about most functionality. PowerPoint, application sharing, audio and video. No mention of application/desktop sharing though, so it sounds like that’d hit your resources hard in a huge conference like this.
The document also includes some interesting stats Microsoft found around how conferences are used on Lync. To find out more, download the document here from the Download Center.